Critical Cisco Secure Firewall Management Center Vulnerability (CVE-2026-20131, CVSS 10.0)

A newly disclosed critical vulnerability affecting Cisco Secure Firewall Management Center (FMC) has been assigned the maximum CVSS score of 10.0.
Tracked as CVE-2026-20131, the flaw could allow an unauthenticated remote attacker to execute arbitrary code on vulnerable systems and gain root-level control of the firewall management platform.
Because FMC centrally manages firewall policies and security controls across an organisation’s network infrastructure, exploitation of this vulnerability could have significant security implications.
What is CVE-2026-20131?
The vulnerability exists in the web-based management interface of Cisco Secure Firewall Management Center.
It is caused by insecure deserialization of user-supplied data, allowing attackers to send specially crafted serialized Java objects to the system.
If successfully exploited, an attacker could:
- Execute arbitrary Java code on the FMC appliance
- Gain root privileges on the underlying system
- Modify or disable firewall policies
- Access sensitive security configuration data
Because the attack can be performed remotely without authentication, the vulnerability has received a CVSS severity rating of 10.0, the highest possible score.
Technical details and affected software versions are available in the official Cisco security advisory and the entry in the National Vulnerability Database.
Why This Matters
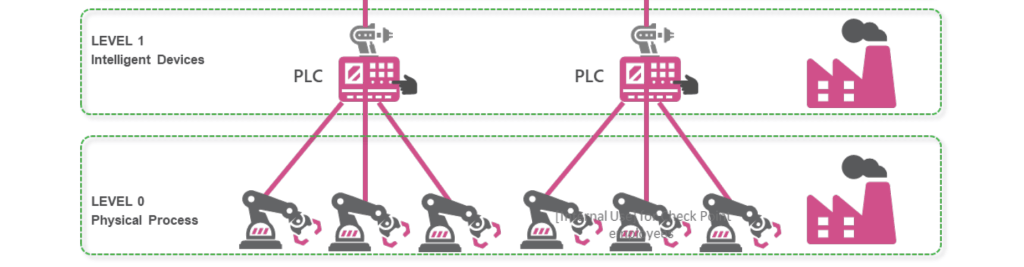
Cisco Secure Firewall Management Center is the central management platform used to administer:
- Firewall policies
- Intrusion prevention systems (IPS)
- URL filtering and threat protection
- Security configurations across multiple firewalls
If the management platform is compromised, attackers may be able to manipulate the security controls protecting the network itself.
In environments where FMC manages multiple firewalls across sites or cloud deployments, this could provide attackers with a powerful foothold for broader network compromise.
Affected Systems
The vulnerability affects Cisco Secure Firewall Management Center (FMC) software used to centrally manage Cisco Secure Firewall deployments.
According to Cisco, the issue impacts multiple FMC software releases, including commonly deployed versions in the 7.x release train. Organisations running on-premises FMC appliances or virtual FMC deployments should verify whether their installed version is vulnerable.
Cisco has released software updates addressing the issue, and administrators should review the official advisory for CVE-2026-20131 to identify the exact affected and fixed versions.
Administrators can check the installed FMC version from the management interface under:
System → Information → Version
For the definitive list of affected versions and upgrade paths, refer to Cisco’s official security advisory.
Is This Vulnerability Exploitable from the Internet?
The vulnerability can be exploited remotely without authentication, but exploitation requires network access to the FMC web management interface.
In most deployments, the FMC management interface is intended to be accessible only from internal administrative networks, which reduces the likelihood of direct internet exploitation.
However, organisations may be exposed if:
- The FMC management interface is directly accessible from the internet
- Remote administration is allowed via VPN or external access portals
- Firewall rules or network configuration unintentionally expose the management service
If the management interface is reachable by an attacker, the vulnerability could allow remote code execution with root privileges on the FMC system.
Recommended Actions
Cisco has released software updates to address CVE-2026-20131, and organisations should treat remediation as a high priority.
Recommended steps include:
- Upgrade FMC to the latest patched release
- Ensure the management interface is not exposed to the internet
- Restrict management access to trusted administrative networks
- Review logs for suspicious access to the FMC web interface
- Implement monitoring for unusual configuration changes
As with any critical infrastructure vulnerability, patching should be scheduled as soon as operationally feasible.
Key Takeaway
CVE-2026-20131 represents one of the most severe vulnerability classes: unauthenticated remote code execution against a security management platform.
Organisations operating Cisco Secure Firewall infrastructure should prioritise patching their FMC systems immediately and review their exposure to ensure management interfaces remain properly restricted.
Recent Posts
Get in Touch With Us
Your trusted partner for secure, scalable and future-ready IT solutions.