Executive Summary
This whitepaper outlines a modern SCADA security design aligned to Australia’s Security of Critical Infrastructure Act 2018 (SOCI). It pairs proven OT patterns—an Industrial DMZ with brokered, recorded jump‑host access; identity separation; and segmented networks—with the Act’s Positive Security Obligations (PSOs): asset registration, mandatory incident reporting, and a Critical Infrastructure Risk Management Program (CIRMP). A practical appendix provides a ready‑to‑use SOCI addendum, including incident reporting workflows, a RACI, and an evidence register template.
Designing SOCI‑Ready SCADA: 2025 Update
Version: 1.0 • 12 Nov 2025
Updated June 2025 based on the latest guidance from the Australian Signals Directorate (ASD) and National Institute of Standards & Technology (NIST)
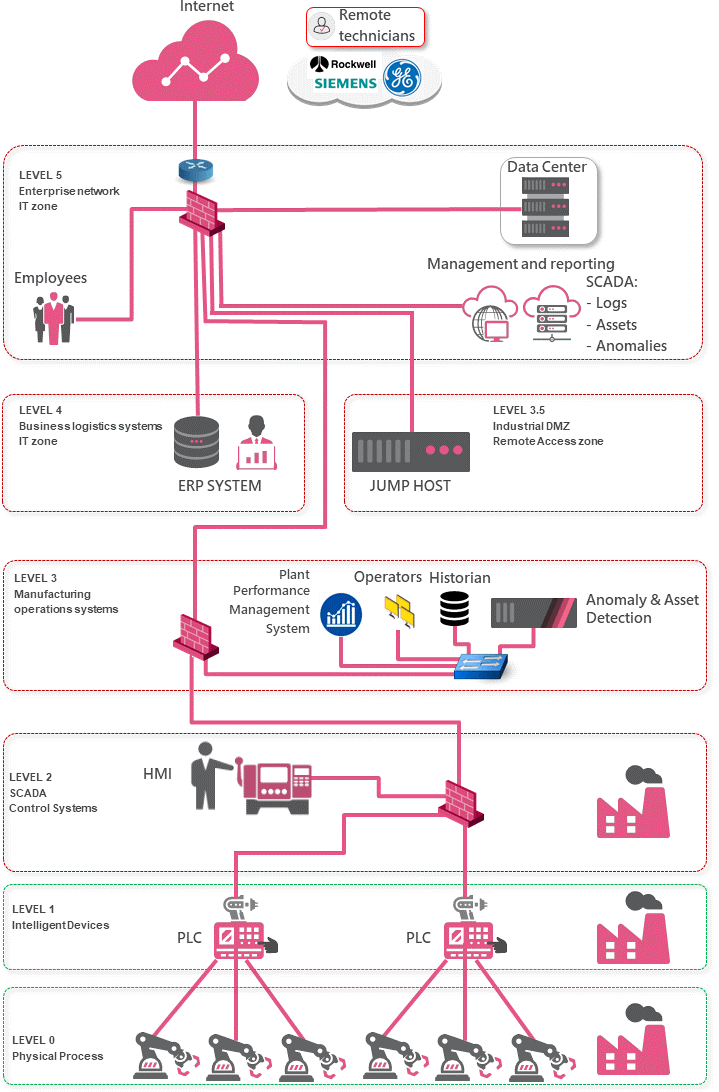
It is vital to take a holistic approach to SCADA security and the broader Operational Technology (OT) / Industrial Control System network design. Every part of the network must be considered, both IT and Operational Technology (OT) and the systems and processes in each zone be investigated, identifying attack vectors and risk, so that the correct security controls can be selected and implemented.
In order to support this holistic approach, the Purdue model should be used. It was adopted from the Purdue Enterprise Reference Architecture (PERA) model by ISA-99 and used as a concept model for Computer Integrated Manufacturing. It is an industry adopted reference model that details the interconnections and interdependencies of all the main components of a typical Industrial Control System, dividing the ICS architecture into 3 zones and further subdividing these zones into 6 levels.
Applying Security to SCADA / ICS / Operational Technology (OT) should dissect the 6 Purdue layers and how they map them to an organisations network. The intent is to gain a detailed understanding of the communication flow between the levels in the Purdue model and how they should be secured.
SCADA Security Design Diagram
Following is a high-level diagram of a SCADA Security Design encompassing the IT and Operational Technology (OT) network environment employing the Purdue model methodology.
It is important to also consider the link between level 2 and 3 as this will vary based on the type of ICS environment. For example:
- Manufacturing plant– A manufacturing plant is typically a single-site, combining both Operational Technology (OT) and IT at the same location.
- Utilities and energy– Utilities providers such as gas, water and electricity are typically distributed environments with many sites communicating back to one or many central facilities over varying medium types. In these scenarios, bandwidth limitations will need to be considered in any proposed architecture.
It is also important to note that at each level of the Purdue model, multiple networks will exist with strict security policies based on their functions. For example, within Level 3 Active Directory, Security Management Servers, Asset Anomaly Detection and Plant Operations System would all be separated and individually secured.
Level 5 and 4: The Enterprise IT Network and Business Logistics Systems
Recommended Security Controls:
The IT network , users and the internet egress point is located at this layer, as such, it is recommended to enable the full Next Generation Threat Prevention feature set on the network level, as you would any network perimeter:
- Security Management Server/s (IT Security Domain)
- Active Directory (IT Security Domain)
- Privileged Access Management (PAM) System (IT Security Domain)
- Firewall (IT Security Domain)
- Separation of perimeter and internal firewalling is strongly advised.
- IPS
- Antivirus
- Antibot
- Sandboxing
- Content Disarm and Reconstruction
- Application Control
- Identity Awareness
- URL Filtering
- SSL inspection
- MFA (Multi-Factor Authentication)
- DDoS Protection
- Endpoint XDR Security
It is critical to ensure a full Endpoint XDR suite is installed on all supporting endpoints (servers, workstations etc.) and that the telemetry is logged and monitored to detect malicious, suspicious and anomalous behaviour.
Where level 5 and 4 assets reside within the public cloud, whether that be on IaaS, PaaS or SaaS, it is imperative that the same security controls are extended to the public cloud environment.
Implementing suitable Network and Endpoint security controls at these levels will help prevent an attacker or malware from breaching the ICS environment.
Level 3.5: The Industrial DMZ
Recommended Security Controls:
- Firewall (IT Security Domain)
- IPS
- Antivirus
- Antibot
- Application Control
- Identity Awareness
- Access to resource within Level 3.5 is controlled based on Identities within the IT Security Domain, however, the authentication of resources within level 3.5 is completed against Active Directory within the SCADA/Operational Technology (OT) Security Domain.
- URL Filtering
- SSL inspection
- MFA (Multi-Factor Authentication)
- DDoS Protection
- Endpoint XDR Security
- Authentication of resources occurs against the SCADA/OT Security Domains Active Directory.
To ensure maximum availability of the remote access gateway allowing for third parties to remotely manage and monitor the Operational Technology (OT) equipment, it is vital to protect the gateway with an anti-DDoS solution.
This design provides a jump server in the industrial DMZ which is commonly a Remote Desktop Server. The VPN Remote Access sessions are terminated on the perimeter gateway in level 5 and are subject to either certificate-based authentication of Active Directory joined devices or RADIUS multi-factor authentication. The gateway terminates VPN traffic, scans it for malware and inspects it for attempted exploitation of vulnerabilities, only allowing RDP traffic from approved source identities to the jump host.
Authentication against the jump host uses a combination of Active Directory credentials and multi-factor authentication for increased security, with authentication occurring against Active Directory within the SCADA/Operational Technology (OT) Security Domain, ensuring a credential compromise of a user account used within the IT Security Domain cannot impact the operations of SCADA/Operational Technology (OT) infrastructure. This jump host is then used to connect to operator workstations in level 3 for remote maintenance work.
This approach is significantly more secure than allowing inbound L3 VPN connections from the internet directly into the ICS networks and significantly reduces the risk of the Operational Technology (OT) network becoming compromised due to unsafe RAS connections originating from third parties.
The jump server itself is protected by the gateway, which will only allow inbound RDP and has the necessary security controls enabled such as IPS, Anti bot, Identity Awareness and Application Control. The jump server should also have a full Endpoint XDR suite such as Check Point Harmony Endpoint or SentinelOne Singularity EDR is installed.
Level 3: Manufacturing Operations Systems
Recommended Security Controls:
- Security Management Server/s (SCADA/Operational Technology (OT) Security Domain)
- Active Directory (SCADA/Operational Technology (OT) Security Domain)
- Privileged Access Management (PAM) System (SCADA/Operational Technology (OT) Security Domain)
- Anomaly and Asset detection and visibility
- Firewall
- Antivirus
- Antibot
- IPS (typically used as a virtual patch to protect the monitoring stations of the operators)
- Application Control (An application control security policy that only allows specific authorized commands to be sent from the operator workstation to PLCs)
- Identity Awareness (Identity Awareness adds an extra layer of security to the policy by only allowing authenticated users (i.e. operators) to send specific commands to devices in Level 2)
- Active Directory/LDAP Authentication of (SCADA/Operational Technology (OT) Security Domain) all systems and infrastructure including SCADA and Plant management systems
- URL Filtering (URL Filtering restricts internet access where required to specific trusted sites, such as the Bureau of Meteorology, Electricity supplier’s outage maps and Cloud Historians)
- SSL inspection
- Encryption of control traffic between operators in L3 and PLC’s in L2 using IPsec to prevent eavesdropping and traffic replay attacks.
- XDR Endpoint protection including Port Protection
Level 2 and 1: Securing Communications Between Levels
Recommended Security Controls:
- Use gateways running IPS to protect vulnerable systems as a virtual patch.
- The communication between level 2 and 3 can be encrypted using IPsec to protect against sniffing and replay attacks.
- A security gateway can be connected to a mirror (SPAN) port on a switch in this level, operating as a sensor and feeding information about asset discovery and anomaly detection to an Asset and Anomaly Detection appliance.
- Customers willing to consider inline security gateways in level 1 can separate local operator workstations and HMIs from PLC’s and RTU’s ensuring no unauthorized commands can be sent to them.
- Appropriate L2 security on switches
- Consider the use of an out of band network solely used for management traffic, signature updates and firmware updates of equipment in this level. Only SCADA protocols should be seen in Level 1.
- Do not allow remote technicians to directly connect to the level 1 network, prefer the use of a jump host in the DMZ in level 3.5.
Level 0: Physical Processes
Recommended Security Controls:
It is recommended to use point to point connections between the intelligent devices in level 1 and the field devices in level 0.
In the case that communication between level 1 and level 0 is over IP, the preference is to use point to point connections. If point to point connections are not possible and Ethernet switches are used in level 0, ensure that appropriate L2 security is enforced: all unused switch ports should be shutdown, MAC authentication should be used on switch ports, consider the use of additional security gateways between Level 1 and Level 0 where applicable. The use of a trusted baseline policy with the application control blade can warn an admin if an unknown command is sent to a field device.
The technologies that S5 Technology Group recommend when deploying the Purdue model are:
- Check Point Quantum Security Gateways
- Check Point Quantum Management
- Check Point SmartEvent
- Check Point Harmony Endpoint Security
- CyberArk Priviledged Access Management (PAM)
- SentinelOne Endpoint Security
- Claroty Asset and Anomaly detection engine
- Multi-Factor Authentication
- Microsoft Active Directory Domain Services
- Microsoft Active Directory Certificate Services
- Arctic Wolf SOCaaS
Operational Technology (OT) / ICS / SCADA Security Design Key Takeaways
Here are some key takeaways of a robust Operational Technology (OT) / ICS / SCADA Security Design:
- Ensure proper segmentation is in place. This is not about having a lot of different VLAN’s or subnets and simply enabling routing between them. It is about having the correct security controls in place between the segments.
- Separate your Security Domains. Separating the security controls, authentication and management of security domains avoids a compromise of one domain resulting in access across an organisations entire infrastructure and systems.
- Threat Prevention is vital. Detection simply informs you that the damage has already been done.
- Intrusion Prevention Systems (IPS) should always be enabled in prevent mode with alerting enabled wherever possible. The Check Point IPS blade provides many signatures that are specifically designed to secure ICS environments
- Application Control within industry leading firewalls provide support for many SCADA protocols down to the command-level and even parameter-level. This allows for the creation of a granular security policy that authorizes only specific commands to be sent to PLC’s and deny everything else.
- Visibility is key. Ensure there is enough manpower to monitor the environment. Tools like SmartEvent, Asset Anomaly Detection and a dedicated SIEM can reveal a lot of information that may otherwise go unnoticed. If you do not have adequate manpower within your organisation, use an outsourced SOCaaS as provided by Arctic Wolf.
Operational Technology (OT) / ICS / SCADA Security Design References
This design has been largely based on Check Point’s Blueprint for Industrial Control Systems, ASD and NIST guidance and with variations based on Client / Asset Owner’s experience in the deployment and management of SCADA environments. Links to these reference articles are below.
- Australian Signals Directorate’s Principles of operational technology cybersecurity
- NIST SP 800-82r3 Guide to Operational Technology
- Check Point’s Blueprint for Securing Industrial Control Systems
- ISA99, Industrial Automation and Control Systems Security
- Wikipedia: Purdue Enterprise Reference Architecture
Appendix A — SOCI Compliance Addendum (2025)
This addendum aligns the design with obligations under the Security of Critical Infrastructure Act 2018 (SOCI) and associated rules, including Positive Security Obligations (PSOs) and, where applicable, Enhanced Cyber Security Obligations for Systems of National Significance (SoNS).
Owner: Chief Information Security Officer (CISO) • Effective date: 12 Nov 2025 • Review: Annual or upon material change.
A0. Glossary & How to Use This Appendix
- RACI — Responsible, Accountable, Consulted, Informed. A simple way to assign who does what.
- CIRMP — Critical Infrastructure Risk Management Program. A written program to identify and manage material risks across four hazard categories: cyber & information security, personnel security, supply chain security, and physical security.
- RCIA — Register of Critical Infrastructure Assets. Government register of who owns/controls critical infrastructure assets.
- ACSC — Australian Cyber Security Centre. Receives mandatory cyber-incident notifications.
- SoNS — Systems of National Significance. A subset of critical infrastructure with enhanced obligations.
- IDMZ — Industrial Demilitarised Zone. A security buffer between IT and OT networks.
- OT / IT — Operational Technology / Information Technology.
A1. Scope, Asset Class Mapping & Roles
Identify in-scope environments, the SOCI asset class, and the Responsible Entity (RE) and Direct Interest Holders (DIH). Confirm PSO applicability and SoNS status.
| Environment / Asset | SOCI Asset Class | Responsible Entity | Direct Interest Holders | PSOs Apply (Y/N) | SoNS (Y/N/Unknown) | Notes |
| SCADA Core (Primary DC) | Critical water asset | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | SCADA servers, historians, app servers |
| SCADA DR/Backup Site | Critical water asset | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | Warm standby; replication |
| Water Treatment Plant (WTP) Operational Technology (OT) Network | Critical water asset | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | Process control incl. filtration, dosing |
| Wastewater Treatment Plant (WWTP) Operational Technology (OT) Network | Critical water asset | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | Bioreactors, clarifiers, sludge handling |
| Remote Pumping Stations & Reservoirs (RTUs/PLCs) | Critical water asset | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | Telemetry/radio, remote control |
| Corporate IT Supporting OT | Supporting critical infrastructure | Licensed Water Utility | As applicable (for example, operator, JV partner, minority owner) | Y | Unknown | AD, jump hosts, Industrial DMZ (IDMZ) brokers |
Action: Replace examples with your actual assets, RE/DIH and confirm PSO / SoNS status.
A2. Register of Critical Infrastructure Assets (RCIA)
The Responsible Entity must submit and maintain asset details in the Register of Critical Infrastructure Assets. SOP:
- Identify changes impacting RCIA data (ownership/control, outsourcing, material topology change, designated contacts).
- Within required timeframes, lodge updates via the government portal and record the submission ID in the Evidence Register (A5).
- RCIA Coordinator (Governance & Risk) monitors triggers from CAB minutes and contract changes.
- Output: Up-to-date RCIA entries and internal log of submission references.
- Evidence: Submission receipts, screenshots, and CAB minutes linked in A5.
A3. Mandatory Cyber Incident Reporting SOP
Report to the Australian Cyber Security Centre (ACSC): within 12 hours for a critical cyber security incident (significant impact on availability of the critical infrastructure asset), and within 72 hours for other reportable incidents with relevant impact.
A3.1 Triggers
- Confirmed or likely disruption to essential Operational Technology (OT) process control resulting in material loss of availability (12 hours).
- Compromise of Operational Technology (OT) jump hosts, Industrial DMZ (IDMZ) brokers, or domain controllers supporting OT, with potential to affect the asset (72 hours).
- Ransomware affecting HMIs/Historians leading to operating mode degradation (12 hours if material; otherwise 72 hours).
- High-confidence exfiltration of ICS configuration or network diagrams increasing risk to the asset (72 hours).
A3.2 Workflow
- Incident Manager (Incident Manager (IM)) performs impact assessment and classifies (Critical / Other).
- Incident Manager (IM) submits ACSC notification via hotline/portal within 12 hours/72 hours and records reference.
- Incident Manager (IM) notifies CISO, Legal, and Executive Duty Officer; Communications prepares stakeholder messaging.
- Post-incident, update the CIRMP risk register and Evidence Register (A5).
A3.3 RACI
| Role | Accountabilities | On-Call Contact | Escalation |
| Incident Manager | Classification; ACSC notification; timeline; evidence capture | Incident Manager (IM) On-Call | CISO |
| CISO | Policy authority; external coordination; board updates | CISO | CEO |
| SOC Lead | Detection; triage; forensics coordination | SOC On-Call | Incident Manager (IM) |
| Operational Technology (OT) Operations Lead | Plant safety; isolation/restore decisions | Operational Technology (OT) Duty Eng. | Plant Manager |
| Comms/Legal | Stakeholder & regulatory comms; legal privilege | Comms Lead / Legal | CISO |
A4. Critical Infrastructure Risk Management Program (CIRMP) Summary
The CIRMP identifies and manages material risks across four hazard categories. Controls from this design are mapped below with assurance and review expectations.
| Hazard Category | Material Risks (examples) | Controls in this Design | Assurance / Tests | Review Cadence |
| Cyber & Information Security | Compromise of remote access; malware propagation across IT/OT; loss of visibility | Industrial DMZ (IDMZ) brokered access; jump hosts with MFA; allow-listing; Purdue segmentation; XDR; SIEM logging | Quarterly access reviews; annual tabletop; backup restore tests | Quarterly; after material change |
| Personnel Security | Insider misuse of elevated Operational Technology (OT) creds; delayed leaver revocation | Joiner/mover/leaver; PAM; background screening per role | Quarterly access recertification; HR-IT reconciliation | Quarterly |
| Supply Chain | Unvetted vendor access; insecure firmware/patch channels | Vendor due diligence; time-bound vendor accounts; session recording; code-signature verification | Annual vendor assurance reviews; spot checks on access logs | Annually |
| Physical Security | Unauthorised access to cabinets/PLCs; device tampering | Physical access controls; cabinet locks; tamper-evident seals; CCTV | Quarterly walkdowns; audit of key/FOB logs | Quarterly |
Testing & Exercising: Run at least one OT-centric tabletop (loss-of-visibility scenario) and one failover exercise per year; record outcomes in A5.
A5. Evidence Register (Compliance & Assurance Records)
| Ref ID | Control / Obligation | Evidence (file/link) | Owner | Last Updated |
| E-001 | for example, A3 Incident report 12 hours/72 hours submission | for example, ACSC receipt # / screenshot | for example, Incident Manager (IM) / CISO | YYYY-MM-DD |
| E-002 | for example, A3 Incident report 12 hours/72 hours submission | for example, ACSC receipt # / screenshot | for example, Incident Manager (IM) / CISO | YYYY-MM-DD |
| E-003 | for example, A3 Incident report 12 hours/72 hours submission | for example, ACSC receipt # / screenshot | for example, Incident Manager (IM) / CISO | YYYY-MM-DD |
| E-004 | for example, A3 Incident report 12 hours/72 hours submission | for example, ACSC receipt # / screenshot | for example, Incident Manager (IM) / CISO | YYYY-MM-DD |
| E-005 | for example, A3 Incident report 12 hours/72 hours submission | for example, ACSC receipt # / screenshot | for example, Incident Manager (IM) / CISO | YYYY-MM-DD |
A6. Systems of National Significance (SoNS) — Conditional Obligations
If any asset is designated SoNS, implement Enhanced Cyber Security Obligations: cyber exercises, vulnerability assessments, incident response plan lodgement, and information provision to CISC as directed. Capture evidence in A5.
A7. Triggers for Re-Assessment
- Operational Technology (OT) network re-segmentation or major plant upgrades
- Introduction of new remote access vendors or managed services
- Ownership/control changes affecting Responsible Entity or DIH status
- Material incidents or near-misses
About S5 Technology Group
S5 Technology Group operates out of multiple locations across NSW and QLD, Australia. We help utilities and essential-service providers design, secure, and operate resilient IT/OT environments—combining architecture, governance, and hands-on engineering.
About the Author
Guy Coble, Principal Architect specialises in Operational Technology (OT) security and critical infrastructure risk. This whitepaper distils practical steps to align design with SOCI obligations while maintaining safe, reliable plant operations.
Publisher’s Note & Disclaimer
This whitepaper is intended for general guidance on aligning Operational Technology (OT) security design with Australia’s SOCI Act obligations. It is not legal advice. Confirm your status and obligations with legal counsel and the Cyber and Infrastructure Security Centre (CISC). Incident reporting timeframes and program expectations are summarised for awareness and should be validated against the latest legislative instruments and rules.
Recent Posts
Get in Touch With Us
Your trusted partner for secure, scalable and future-ready IT solutions.




